Are the fans on your air-gapped system sound a little off? Maybe they are rapidly changing speeds? You better roll back the security footage and start the facial recognition scans for any signs of Ethan Hunt and team!
Researchers at the University of Negev have created a new method of acoustically extracting data from a system without the use of speakers. The new method named fansmitter can extract data from air-gapped systems by taking advantage of the sound emitted from the system fans that are then picked up by a nearby cell phone’s microphone. According to researchers, CPU and chassis fans are the ideal to leverage because they are easy to control via software.
At the most covert frequencies and least likely to be detected, data can be transferred at three bits per minute as long as the receiver is within three feet. This translates to about 1 byte every three minutes or one character of a document. However, an attacker can increase the speed of the transfer to up to 600 bits per hour.
Previous attacks identified against air gapped systems have lead to policies of removing sound cards because of “AirHopper” which is a method of using FM to covertly transfer data. But those are speakers and we can’t easily remove the system fans!
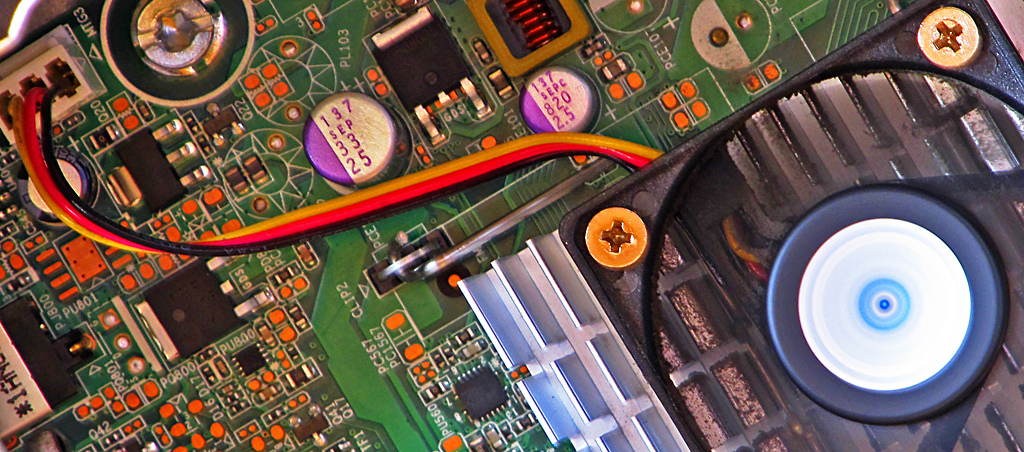
One of the proposed countermeasures proposed was switching to liquid cooling. While this may not be financially advantageous, this seems to be the surest way to prevent this attack. Other methods included zoning air gapped systems from any other electronic equipment, running noise detection hardware, and using a signal jammer.
Physical security is often the most difficult to safeguard. The next time I’m working on a server, you can be sure I might just be paying a little extra attention to the sound of those fans!